Organizations rely on third-party vendors for a variety of services, from payroll processing to HVAC maintenance to information technology services. Every vendor relationship brings potential security risks, and shortfalls in one vendor can compromise sensitive data throughout the supply chain. Vendor management programs, service level agreements, and long-term monitoring are valuable tools for managing vendor cyber risks.
What Is a Vendor Management Program?
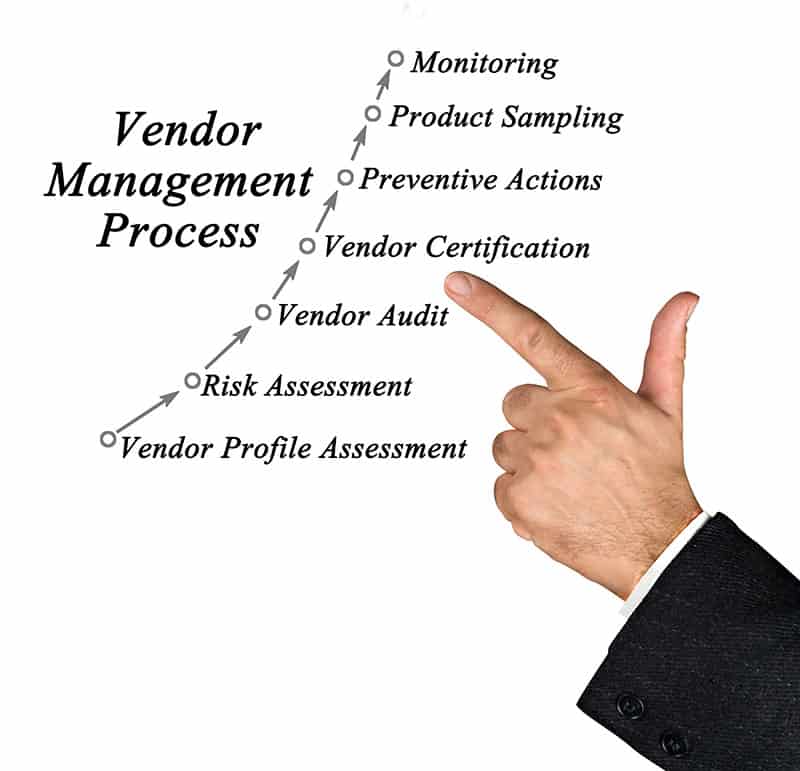
A vendor management program provides a system for monitoring and mitigating third-party risks (cyber or otherwise). It allows an organization to rank its vendors according to cyber risk and monitor vendors for changes in data protection and control.
Vendor List
You’ll need to make a list of all vendors who have access to your network or sensitive data. Include all types of vendors, from large IT service providers to local maintenance contractors. Find out and include the types of data security controls they have in place.
The next step is to classify the vendors in your list according to the risks they present to your data. This will help you determine how closely you need to research and monitor each vendor.
Due Diligence
Due diligence is research that helps you identify the risks associated with each vendor. Your research should include cybersecurity issues such as the vendor’s data controls and incident response protocols. From this information, you can determine the steps you should take to manage risks, such as implementing contracts that require certain data controls.
Long-Term Approach
Your organization’s relationship with every vendor will change over time. A vendor management program must be able to adapt to the inevitable changes in personnel and business strategy. Security ratings and other technologies can help you monitor changes in vendor behaviors. Contractual agreements will need periodic review to ensure best practices in protecting data.
Protections in Service Level Agreements
When it comes to managing third-party cyber risks, a written agreement is indispensable. Each party must know their responsibilities regarding data protection. The service level agreement (SLA) with each vendor should include language that covers risk management.
The SLA should contain a clause that addresses third-party responsibility for data security. Audit requirements can assist in monitoring third parties for security vulnerabilities and deficiencies. Cybercriminals are very creative, so you don’t want to leave anything to chance.
Consequences of Not Managing Third-Party Vendors
It only takes one click of a malicious link to set a far-reaching breach in motion. That is exactly what triggered the infamous Target data breach in 2013. One of Target’s HVAC contractors was compromised when an employee clicked a link in an email phishing attack. When the employee logged in to work on Target’s HVAC system, cybercriminals gained access to Target’s POS terminals and the personal data of thousands of customers.
Another well-known incident is the 2018 breach of the reservation system of Starwood hotels, owned by Marriott. Criminals had taken control of an administrator’s account and gained access to the credit card and passport numbers of millions of customers. Even more alarming was the fact that the breach wasn’t detected until four years after it occurred. Marriott had cut Starwood’s IT and cybersecurity staff, and had failed to update its reservation system after acquiring Starwood.
These incidents demonstrate the importance of actively managing third-party cyber risks. The Target and Marriott breaches show that constant vendor monitoring and updating are crucial for protecting the data of an organization and its customers.
Active Vendor Management Is a Necessity
Without due diligence and risk management, any organization can fall prey to a data breach. When the breach originates in a third-party vendor, it can affect sensitive data up and down the supply chain. An adaptable, active vendor management program will minimize cyber risks and protect data now and in the future.
It is common for organizations to outsource vendor management to a trusted partner such as Interactive Security in order to setup and maintain the ongoing program.
References:
https://www.bitsight.com/blog/how-to-develop-a-vendor-cyber-risk-management-framework
https://www.pcisecuritystandards.org/pci_security/
